What is DNS?
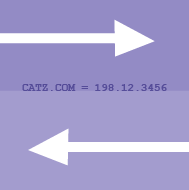
DNS is short for "Domain Name System." That's Internet-speak for a protocol that matches easy-to-remember website names with their actual numerical address on the world-wide web.
Think of DNS as being like your phone’s address book, where you can look up specific numbers for people - or in this case websites - that you want to reach. Others compare it to a giant map that shows exactly where on the web every particular website lives.
For example, "voanews.com" is the name of this Internet domain and what you type in your browser. That may be easy for humans to remember, but it doesn't really mean anything to the web servers that are routing you from site to site.
This domain's actual Internet address under Internet Protocol version 4 (IPv4) is "152.75.191.91" That's not a secret, but it's not easy to remember. Thus to help out, the DNS database matches standard domain names - like voanews.com - to their actual location on the web so that your IP server can connect with that exact site.
How it works
Everything on the public Internet - including your Internet service provider or ISP - has a unique DNS address. To find out the DNS of the server you're using right now, just go to your "cmd" function and enter "ipconfig/all" and you should see it identified as a series of numbers and periods.
It's also important to remember that there isn't just one DNS record, but many, many copies distributed throughout the web. It's these two factors, and the de-centralized structure of the Internet, that create loopholes that governments and individuals alike can exploit.
Without getting lost in the technical details, an ISP or government can "poison," or alter, particular DNS records, re-routing web traffic from the requested sites to favored ones. For example, a user in country X may try to visit "voanews.com", but a poisoned DNS list might redirect that user to a spoof site, or a page announcing the block, or merely to the dreaded "404 Not Found" page, thus blocking all incoming traffic.
That said, individuals can also exploit some of these loopholes to get around government DNS poisoning. There are many DNS services you can use, but let’s focus on one of the most popular: Google DNS.
Google maintains its own DNS list that's freely available to anyone who wants to use it. As much as possible, they say, it represents an accurate map of websites and their authentic IP addresses.
This Google list is available at two IP addresses: "8.8.8.8" and "8.8.4.4". By changing the settings on your computer or smartphone, you can instruct your device to use this non-poisoned DNS list to access the sites you want, but that country X may not want you to see.
It can be a little tricky, as different computer operating systems have different steps you need to take. That's why Google has a complete how-to sheet here. However, once you're connecting with Google's DNS, you are slipping around the poisoned lists, and evading the blocks.
A DNS-poisoned block is a relatively primitive tool. It's often the first response of panicked, or less-tech-savvy government. Think of it as a phony road sign posted by a government telling drivers the road ends ahead. Drivers armed with the right map can clearly see the road continuing, and carry on. But governments determined to block traffic can do more than just post signs...and often do.
Possible drawbacks
In the end, using DNS can be a handy trick to work around sudden Internet blocks, but in practice it can be a short-lived tool. Internet users who live in nations that exert a heavy censorship hand will need more tools to get where they want to go.
It’s also very important to remember that there is no anonymity in using DNS. So if you think you’re being monitored, governments and hackers can still see everything you’re doing online.
DNS can be an easy and fast way to slip past censors and view blocked sites, but offers no enhanced privacy. It’s more of a trick than a tool, thus often has limited use.