Tor is one of the oldest and most popular circumvention applications available. And with good reason. That’s because Tor rates among the most secure and effective ways of guarding your anonymity online, while also helping you evade government censorship. Here’s what it is, how to use it, and how it might help you online.
What Is Tor?
Tor is shorthand for “The Onion Router” with “onion” serving as a helpful analogy for how Tor works. Think of it like this: just as onions are composed of many layers, Tor employs a nested web of private computers, called nodes, that route and encrypt your Internet traffic through the Internet. It’s complex and redundant, and that provides strong protection against government snooping.
The Tor concept grew from highly technical research conducted by DARPA in the 1990’s and was originally funded by the U.S. Office of Naval Research. Since then, its support base has evolved to include, VOA’s parent agency – the Broadcasting Board of Governors.
Introduced in 2002, several new versions of Tor have since been released, each tightening potential security gaps that governments might (or did) exploit. Most importantly, thousands of volunteers scattered across the globe form the Tor backbone, creating a diffuse “under-the-radar” private network that scrambles data and combats eavesdropping and blocking.
How TOR works
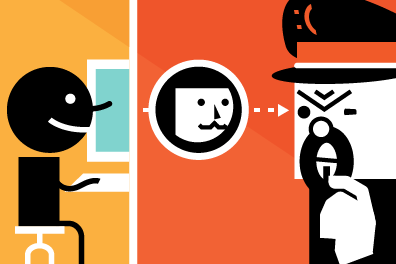
Ordinarily when you visit a website, data is routed from your computer to your target through the global network of public servers that create the World Wide Web. By design, that network is largely open, allowing traffic to pass smoothly from one computer to another. However, that open design also leaves users vulnerable to a variety of security holes.
In contrast, from the moment they go online, Tor users funnel data exclusively through a series of three random Tor nodes – the “entry”, the “relay” and the “exit” – each with its own unique encryption key. Because of the three node nesting, no single computer in the Tor network knows either the ultimate source or destination of the traffic, or even the other computer’s encryption keys, shielding users identities.
The anonymous bouncing of traffic through the Tor sub-network has proven remarkably robust and challenging to crack. Sending data through Tor is like playing a cat and mouse game in which the mouse is hidden three-times over, making the cat’s hunt that much more difficult.
How can Tor help me?
Tor can be helpful when it comes to circumventing blocks and firewalls, but its best use is as an anonymizing tool to protect your activity from external monitoring. Let’s say you’re concerned about the government monitoring what you do online. Once you download the Tor bundle onto your home computer, you can access the Internet to visit sites, upload and download and send email or chat online all while remaining anonymous. Also, the large number of Tor volunteer servers around the world makes blocking Tor a challenge. That means while a site like Facebook or Google might be blocked in your nation, you can route around those blocks using the anonymous Tor network.
Possible drawbacks
Tor is effective, but it’s no guarantee of complete anonymity and circumvention. The volunteer Tor network itself appears largely immune to all but the highest level hacking, but bad actors can exploit security holes on either the user or target end.
Standard browsers such as Firefox, Chrome, Internet Explorer and others each have unique security vulnerabilities that can be used to gather your personal information.
That’s why Tor users are strongly encouraged to use a special downloadable browser that comes bundled with Tor, rather than their own standard browser. The Tor bundle also blocks third-party plug-ins like Java and Flash that are not encrypted and can serve as a gateway for online spying.
Users computers themselves can also be infected and exploited directly with malware and spyware; this is one of the techniques the NSA reportedly employed to try and crack Tor user’s identities. This makes Tor considerably less secure in a place like an Internet café, where spyware can easily be installed.
It’s also very important to remember that while your identity is shielded from spying eyes, your ultimate end destination is not. As soon as data leaves the Tor network, it’s once more public and vulnerable. That means target websites may still be blocked or monitored, and if you send anything to another individuals, they, too, will be public.
A good way to address this is to use Tor in combination with a VPN – a secure network - on the exit side. That will protect you, and tunnel your data to your target.
The bottom line
If you want strong privacy protection, and a helpful circumvention tool, Tor is a great choice.
However, it’s complex and can considerably slow down online browsing, so easily frustrated users may want to consider another tool. And for what it’s worth, in a top-secret NSA document leaked by Edward Snowden, NSA analysts called Tor “…the King of high secure, low latency Internet Anonymity,” adding “there are no contenders for the throne in waiting.”